When talking with businesses about the advantages of connecting telemetry from assets to the cloud, the primary concern raised is data security. Protecting connected assets – and operational data by extension – should always be taken seriously, but strong defenses often come at great expense. The dangers of connecting high-value assets to the Internet without stringent security measures is self-evident, and customers expect to incur commensurate costs in exchange for proper safeguards.
For assets of lower value, the danger is not as obvious. Yet attacks exploiting inexpensive, everyday assets are responsible for several high-profile breaches – news stories abound of IP camera vulnerabilities, unsecured home IoT devices, and many more. No matter its value, any compromised connected device can provide access to the entire network, such as the fish tank that gave thieves access to gigabytes of Casino data. It used to be common practice to lock down industrial embedded devices as tightly as possible, reduce the attack surface as much as possible, and perform updates as rarely as possible (if ever). Nowadays, the evolution of the connected device landscape has rendered these conventional practices obsolete while presenting new security challenges.
To address these emerging threats Microsoft developed Azure Sphere, a secured microcontroller technology. Integrated into a broader solution, it’s capable of delivering significant value to businesses working to transform operations by connecting devices and making systems intelligent.
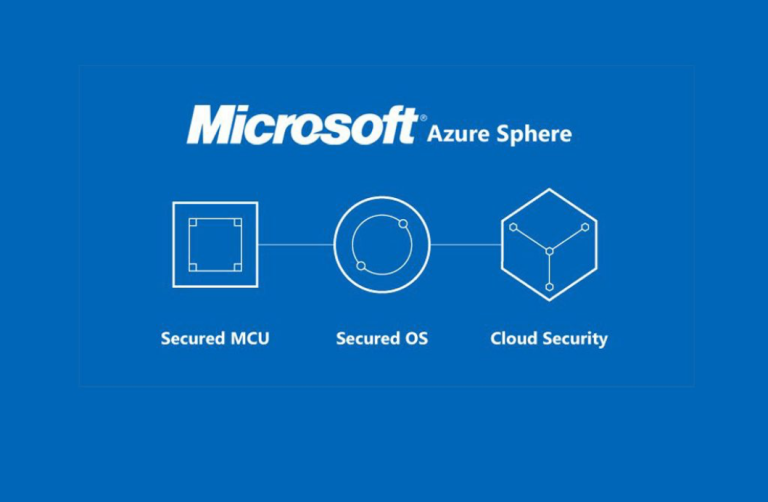
End-to-end security from MCU to cloud.
What is Azure Sphere?
Non-IT professionals may find some of the more technical aspects of Azure Sphere difficult to understand. The primary takeaway is that Azure Sphere has security built into its DNA. Furthermore, the best security practices are integrated into a proven end-to-end solution. From the design and manufacture of the microprocessor, to communications with the supporting cloud service, to the ongoing delivery of operating systems (OS) and other software packages. By building state-of-the-art security into all aspects, Microsoft significantly streamlines security design, implementation, and testing for a solution overall – expediting integration and delivery considerably.
The primary takeaway is that Azure Sphere has security built into its DNA.
Microsoft’s experience securing Windows and XBox against hackers prompted a great whitepaper (The Seven Properties of Highly Secure Devices). In it, they identified the features that a highly-secure network-connected system must have, which formed the basis for creating Azure Sphere and providing secured microcontroller solutions. Namely, these foundational elements are:
- Hardware-based Root of Trust: crypto keys generated and protected by hardware.
- Small Trusted Computing Base: private keys stored securely, self-protecting software layers.
- Defense in Depth: Multiple mitigations against each threat.
- Compartmentalization: Hardware-enforced barriers between software components.
- Certificate-based Authentication: Signed certificate proving device authenticity.
- Renewable Security: Software update mechanism, revocation of compromised assets.
- Failure Reporting: Device reports failures/attacks to cloud-based analysis system.
In 2018, Microsoft announced the Azure Sphere system, designed to meet all seven properties for low-cost devices using a combination of:
- Secured microcontroller design: this consists of multiple cores on a single die, the OS and applications run in an ARM Cortex-A core, and there are one or more ARM Cortex-M cores for real-time applications (either an RTOS such as ThreadX or “bare-metal” code). Hardware firewalls enforce separation between software components, Microsoft’s “Pluton” security system runs as part of the secure boot of the device and provides the hardware root of trust.
- Secured Linux operating system: the application platform (Cortex-A core) runs the Azure Sphere OS, based around a secured Linux kernel using the Pluton security system.
- Cloud security service: provides device attestation and authentication, and software updates to operating system and application software.
This is a fascinating development for Microsoft, just a few years ago it would have seemed unthinkable for them to create either a Linux-based system or a microcontroller design. Shows just how far they have evolved, and how seriously they take IoT security.
How do I use Azure Sphere technology in my device?
There are several options available:
- Design an Azure Sphere chip into your device: include an Azure Sphere chip into your device to provide secure cloud communications. At the time of writing, the MediaTek 3620 is available, with an NXP iMX8 design in the pipeline. This is suitable for device OEMs wanting to build secured communications into their next product revision.
- Design an Azure Sphere module into your device: Avnet, AI-Link and USI have ready-made modules with the Sphere chip together with communications mechanisms which make it easier for device OEMs to build Sphere technology into their devices. Pre-certification of wireless communications in a module can help speed development.
- Use a “Guardian Device” to connect existing equipment securely: introducing a standalone add-on box containing a Sphere chip allows legacy equipment to be connected, sometimes referred to as “brownfield” devices. Used in this way, the Sphere module acts as a secured gateway between the public Internet and the private local network or device.
This Guardian device provides a great way to extend the life of existing equipment, to connect legacy or dumb devices to the Internet to begin receiving the benefits of IoT.
But Azure Sphere-enabled devices are just the start. In practice, realizing the full business value of this technology requires a broader, integrated solution. By incorporating connected devices outfitted with Azure Sphere into intelligent systems, businesses have the opportunity to transform operations while reinforcing security and accelerating time to market.